Let's get
started
Let us show you how Omada can enable your business.


Discover what role modelling means, its significance, and how Role-Based Access Control (RBAC) models work in our comprehensive guide.
Large environments need a structured role model to keep access decisions clear and repeatable. The guide links role modeling to Role-Based Access Control (RBAC) in Identity Governance and Administration (IGA) and walks through defining roles, mapping entitlements, and validating with business owners to simplify provisioning and audits.
Managing user access rights efficiently and securely is crucial for organizations of all sizes. Role Modeling and Role-Based Access Control (RBAC) have emerged as powerful tools in Identity Governance and Administration (IGA) to streamline access management, enhance security, and ensure compliance. This guide will walk you through the essentials of a role model, define what a role model is and its role in IGA, and how Role Modeling can benefit your organization’s identity security strategy.
The role modeling meaning for businesses isn’t as easy to explain as role models in the traditional sense, but it’s just as important to an organization to have role models as it is to have a role model in life.
Role modeling in Identity Governance and Administration (IGA) involves creating, managing, and maintaining sets of predefined roles to streamline access management, enhance security, and ensure compliance within an organization. It is an integral part of working towards best practices for organizations to keep identities in conformance with ‘least-privilege‘ to perform their jobs. When done properly, a role based access control model can help grant access and establish a role governance process, but if the role model is not sufficiently developed, the entire Identity Governance & Administration (IGA) project will be delayed.
While identity management modeling programs can be difficult to define and maintain, they are critical for an organization’s ability to oversee who is doing what, and why—not to mention the efficiency gains from automating the granting and revoking of default role access rights to joiners, movers, and leavers. Here’s how to get buy-in and kickstart an efficient and effective role modeling.
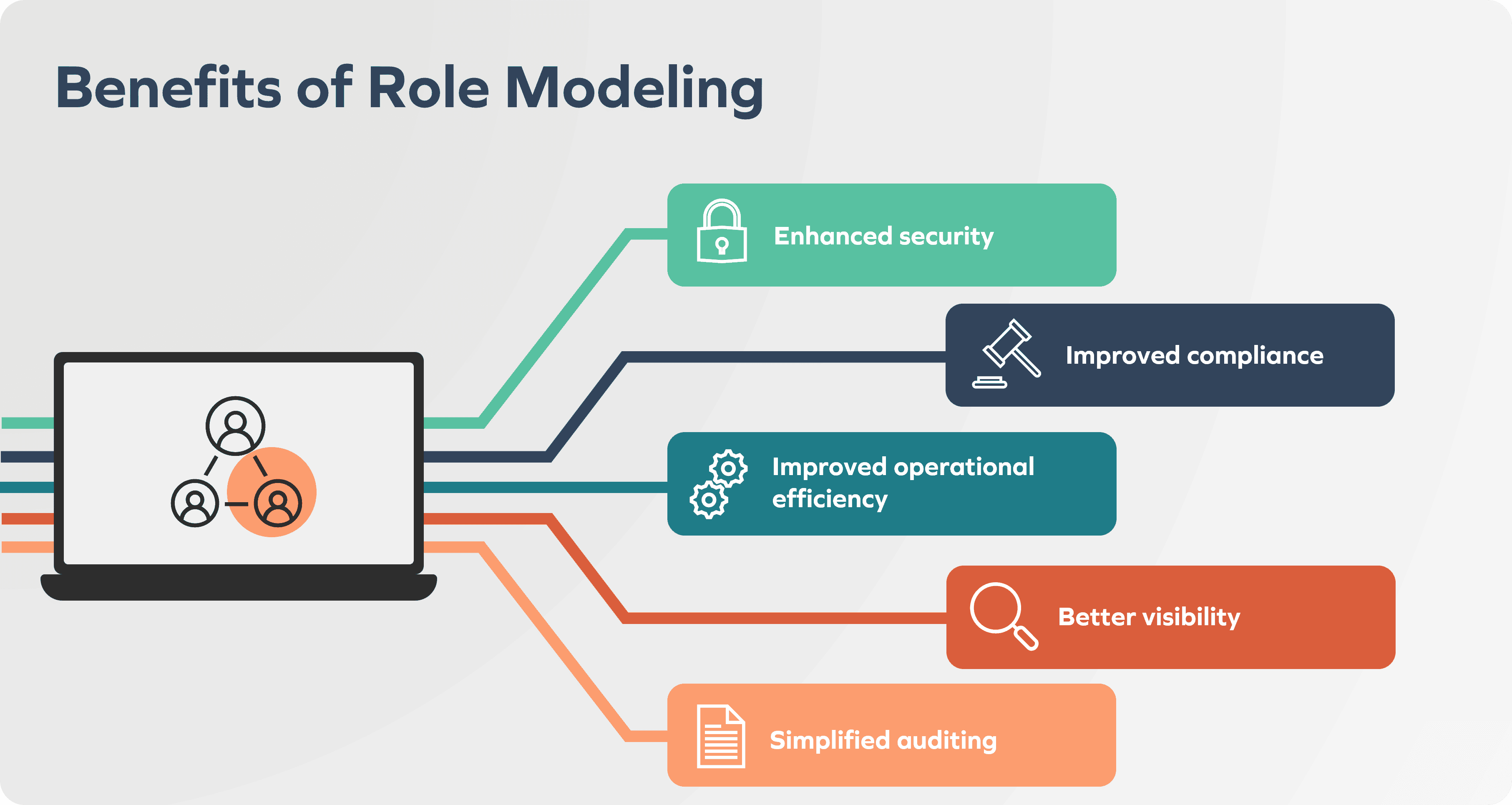
Role modeling is fundamental for Role Based Access Control (RBAC), as it determines which roles need access to what resources within an RBAC model. This allows for:
A role is an aggregate of policies, entitlements, and business contexts that come together as a named function that groups similar types of identities. Ideally, roles would relate to certifiable traits like job titles, or organizational responsibilities, but it isn’t always this simple.
Roles can range from abstract to completely opaque if not defined properly. In either case, roles are easier to manage than individual access rights, as similar identities can be assigned the same roles depending on what they need to perform their daily functions. This can mean grouping application-specific entitlements like Lightweight Directory Access Protocol (LDAP), email, or application privileges.
The most common role types tend to be application roles that grant access to a single application or system, technical roles for people that need to perform administrative tasks, and business roles that relate to one’s position or work responsibility. While these do seem like easy categories for characterizing role modeling, roles are challenging to design, harder yet to maintain, and hardest to delete. This is due to the complex web of entitlements that are woven throughout every organization.
The way that roles are determined and role modeling is approached will vary from situation to situation depending on the different type of access control that a business decides to employ as their solution.
Here are some RBAC model examples and how they affect the categorization of roles and access within an organization:
Role modeling is a constant exercise that requires an iterative approach supporting the introduction of new roles, modification and review of existing roles, and the decommissioning of existing roles—all of which vary in complexity.
Before getting into the weeds, in any project the first checkpoint is to determine the goals and scope. Questions asked will range from, what are we trying to accomplish from a compliance, security and efficiency perspective? What are the applications, identities, and contexts that are in scope? And plenty more.
The next step is figuring out the big question: what does good enough look like? Ideally, the ratio of identities to roles is as far away from 1:1 as possible so that roles can be fit to purpose and scale, and that each identity is not its own role.
Roles should include baseline access rights (sometimes referred to as ‘birthright’), as well as other commonly required access, but as roles become more bespoke, it becomes more challenging to fit them to scale. Any good role model will need to be fit for growing and evolving business needs.
After defining what the initiatives are, defining the role model by principles, role types, model hierarchy, and use cases (like request and approval scenarios), it is important to set guidelines for how the role model will take form.
Critically, before diving in to design the roles themselves, an organization must verify the role model by identifying the stakeholders and getting their buy-in. Typical stakeholders that should be included are application owners, data owners, IT administrators, auditors, and security team leads, among others. Now that the groundwork and project plan has been laid, we can look at how to create the roles and role models.
In this phase, we look at designing role management processes, including how to create a new role, change or revise roles, delete old roles, and constantly evaluate role quality.
In producing new roles, organizations are encouraged to both mine and design roles. Mining tools support the analysis and establishment of roles and privileges when it is run on live production entitlement data to determine roles that fit each individual organizational hierarchy.
However, please note that you cannot just plug in a mining tool and suddenly have role modeling complete. This tool needs to be married with processes that fit the business needs of your organization, including things like how this meets various compliance measures, and why certain entitlements are aligned with specific jobs. The desired data gathering can be based on identity types, templates, organizational attributes, and more to help craft the role.
After these roles have been created, they are validated by the appropriate stakeholders and listed out with potential assignment policies.
Throughout a role’s lifecycle, careful attention needs to be paid to role management. In order to do this, regular role reviews are needed periodically to ensure that roles remain relevant and appropriate. If there’s an opportunity to consolidate and merge roles, then these should be identified to prevent role explosion, and keep the number of roles that are in the RBAC system manageable.
It is important that organizations establish processes for decommissioning roles that have become obsolete within an organization and need to be retired, and also implement a formal change management process for requesting and approving role changes.
Monitoring and reporting should be done using analytics to properly track a role’s usage and effectiveness.
After roles have been defined and vetted, we can then integrate them into access management processes. These include access requests and approvals (i.e., a business user raising their hand to request access and then the request being automatically routed to their manager for approval), mitigation of risk, and other business descriptions that help quickly fit roles to more and more identities.
Having processes in place to audit roles, and to recertify those roles that are being used, are critical to maintaining good role model quality. They also help to flag compliance exemptions for when there are combinations of access rights that do not seem to make sense. Role modeling can also help by reducing the number of questions asked in a recertification, simply by bundling entitlements into a role and inherently dropping some questions.
While role modeling is crucial for a business’s cybersecurity, it can also be tricky to implement. Some of the biggest challenges that organizations need to overcome are:
This is when there are too many roles within an organization to be able to be managed. This can be prevented by efficient role management that prioritizes the consolidation and decommissioning of roles whenever possible.
As organizations change, so do the resource needs of different roles. This requires continuous monitoring and rapid adjustments to reflect shifting responsibilities and company structure.
Balancing granularity with manageability involves finding the sweet spot where roles are detailed enough to ensure proper security without becoming too overly complex to administer.
Buy-in from both users and IT staff is crucial for the adoption and adherence to new role standards, but information and training sessions can help to mitigate staff resistance.
When implementing role modeling in an organization, it’s always important to start with a pilot project to help evaluate factors like feasibility, duration, cost, and risk, before undertaking a larger RBAC project.
Key stakeholders should be involved from the beginning to try to mitigate any internal resistance to changes and to make sure that their needs are properly addressed by the new RBAC solution.
As we have mentioned, it is crucial to continuously review, monitor, and refine roles to avoid issues like role explosion.
To do all of this, organizations need a combination of both top-down (i.e., executive mandates and strategic alignment) and bottom-up (i.e., user feedback and role mining) approaches.
Role modeling is also incredibly helpful for ensuring that companies comply with regulations like General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), and Sarbanes-Oxley Act (SOX). By defining clear access controls, organizations can ensure that only authorized personnel have access to sensitive data, which is a key requirement for compliance.
As artificial intelligence (AI) and machine learning (ML) become increasingly more popular, there is no question that they will both play a part in role recommendations. These technologies can predict the most appropriate roles and permissions for users based on their job functions, potentially improving accuracy and reducing administrative burdens.
Additionally, dynamic role assignment can adjust user roles in real-time based on context, such as the user’s location, device, time of access, and the nature of the task being performed, allowing for more granular and responsive access control, ensuring that users have the right permissions only when they need them.
Finally, by integrating role modeling with zero-trust security companies will be able to more confidently prevent unauthorized access.
An effective role modeling approach should also aid in the effort of assigning and unassigning roles automatically, manually, or based on rules. The goal is to implement a role model that makes sense for each organization, where business users maintain business productivity, and IT teams maintain governance and visibility into who has access to what, and why.
Most roles should be assigned using the access request process so that as access requirements come up, they can easily choose from a list of roles that are easy to comprehend with smooth approval processes for administrators, but each business has different ways of maintaining productivity.
The goal is to come up with a role model that meets their needs.
Omada is a market leader in modern IGA and has been helping organizations implement foundational role modeling principles to help enhance efficiency, meet compliance mandates, and increase security.
Want to learn more about identity security? Read more, or book a meeting with an expert today.
FREQUENTLY ASKED QUESTIONS
Role modeling in Identity Governance and Administration (IGA) means creating, managing, and maintaining predefined roles that determine which resources each type of user can access. A sound role model supports least privilege and keeps identities in conformance with the access they need to perform their jobs across many applications.
Role modeling provides a structured foundation for Role Based Access Control (RBAC) by mapping roles to resources in a clear and repeatable way. This clarity strengthens security, supports regulatory expectations, and gives better visibility into who has access to which data and why those entitlements exist.
Common role types include application roles that grant access to a single system, technical roles used for administrative tasks, and business roles tied to positions or responsibilities. These categories help organize complex webs of entitlements but are hard to design, maintain, and retire without continuous governance.
Role modeling is an ongoing exercise that introduces new roles, adjusts existing ones, and retires those that no longer fit. Organizations need to get organized around their chosen access control approach, use examples of Role Based Access Control (RBAC) models to guide grouping, and refine roles as structures and risks change.
Artificial intelligence and machine learning are expected to support role recommendations by predicting appropriate roles and permissions from job functions. Dynamic role assignment and alignment with zero trust security will let permissions adapt in real time based on context such as location, device, and task, which improves precision and control.



