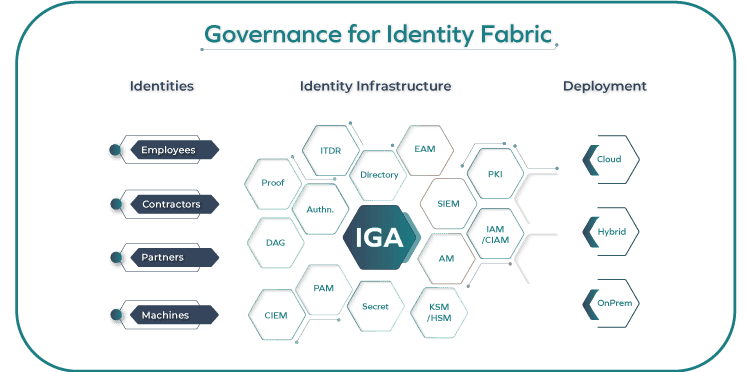
Reshape your IAM strategy with a focus on identity fabric governance. Discover how an identity governance-first mindset and use case-driven evolution can revolutionize your approach to governance.

- Identity everywhere: Extend identity governance to any application including third-party applications and mobile devices for a frictionless experience.
- Out-of-the-box connectivity: Connect and configure to more applications with minimal effort and no coding requirements with our Connectivity Framework.
- Identity-first security: Improve the visibility of risk and compliance by unifying information from the security landscape through bi-directional context exchange.
- Decision automation: Leverage automation and intelligence to support human decision-making and automate wherever possible.